Whether you are upgrading your company computers as part of a scheduled refresh or relocating to new commercial premises, you will probably be left with unwanted or non-functional IT hardware.
Old computers contain large quantities of sensitive data, so care should be taken to ensure that data is completely eradicated when disposing of them. To facilitate this process and ensure compliance with data protection law, companies often hire a data destruction service, such as Absolute ITAD, to protect themselves from potentially costly and damaging data breaches.
What Is The Data Destruction Process?
Data destruction makes the data on the device inaccessible to prying eyes and can be achieved by physical, electronic or digital processes.
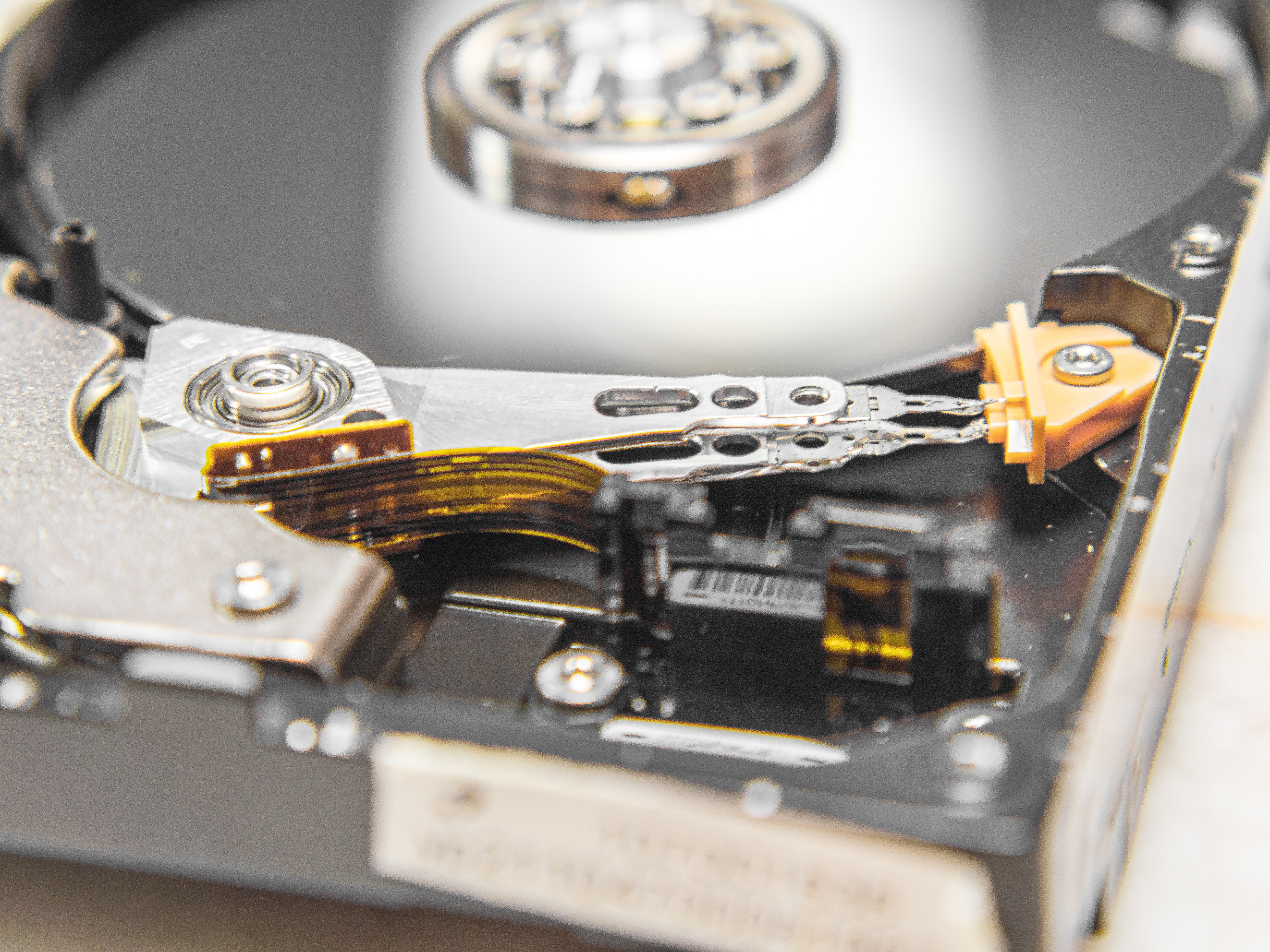
Data-bearing devices, such as mobile phones and hard drives, can be physically destroyed by methods such as degaussing and data shredding. Degaussing removes or reduces the hard drive's magnetic field, so the data it contains is no longer retrievable. Data shredding can be carried out on-site by IT professionals using DataRaze, but this is a labour-intensive procedure.
Data can also be destroyed mechanically by crushing, shredding, or chopping data-bearing material into pieces as small as 6mm. These pieces are then refined further, completing the process of data destruction. A licenced data destruction company will retain records of the shredded items for your audits.
Why Is Data Destruction So Important?
For legal, ethical and environmental reasons, your data must be disposed of responsibly and securely. Data destruction is a very specialised job and should be carried out only by accredited vendors, such as an ADISA accredited IT asset disposal company.
So-called "free" IT recycling services can pose multiple risks unless you are extremely circumspect in your choice of vendor. In some cases, for example, donated IT assets may be refurbished and sold in developing countries – either for private gain or on behalf of a charitable cause - without secure data sanitisation. This can allow the data to be recovered using the right software. In addition, there are many examples of data-bearing devices being disposed of improperly and being found in rubbish dumps and other insecure locations. This can potentially harm the environment, and in addition, the owners of the data-bearing assets are at risk of a costly data breach.
Even if the data-bearing devices have stopped working or are faulty, the information on the hard drive can usually be recovered. Therefore, data destruction is the optimal way of ensuring that no sensitive data can be recovered from discarded devices.
An Alternative To Data Destruction: Data Erasure
As the name suggests, data erasure achieves the same result as data destruction but by securely erasing data beyond recovery rather than by destroying the physical asset. This method can offer logistical and environmental advantages, as the computer or device can be archived or reused internally, or safely donated or resold.
Specialist data erasure software also provides a comprehensive audit trail of all data erasure procedures to ensure that your company and your data remain secure and protected.
Professional Secure Data Sanitisation
At Absolute IT Asset Disposals, we provide a premium secure asset disposal and data sanitisation service for companies and organisations seeking a range of IT asset disposal and supply chain management services. Our experience, skills and accreditation allow us to handle our clients' sensitive data responsibly and carefully and dispose of it legally and sustainably.
Do you require more information? Please download our free Guide To Mobile Data Sanitisation to find out more.
Image Source: Unsplash












