Cyber-attacks and hackers are becoming more and more sophisticated, and a recent ransomware attack on an NHS IT provider has left many wondering how robust data systems truly are against such dangers. So what happened, and how can you protect yourself from a similar occurrence?
6 IT Components That Could Run Out Within A Century
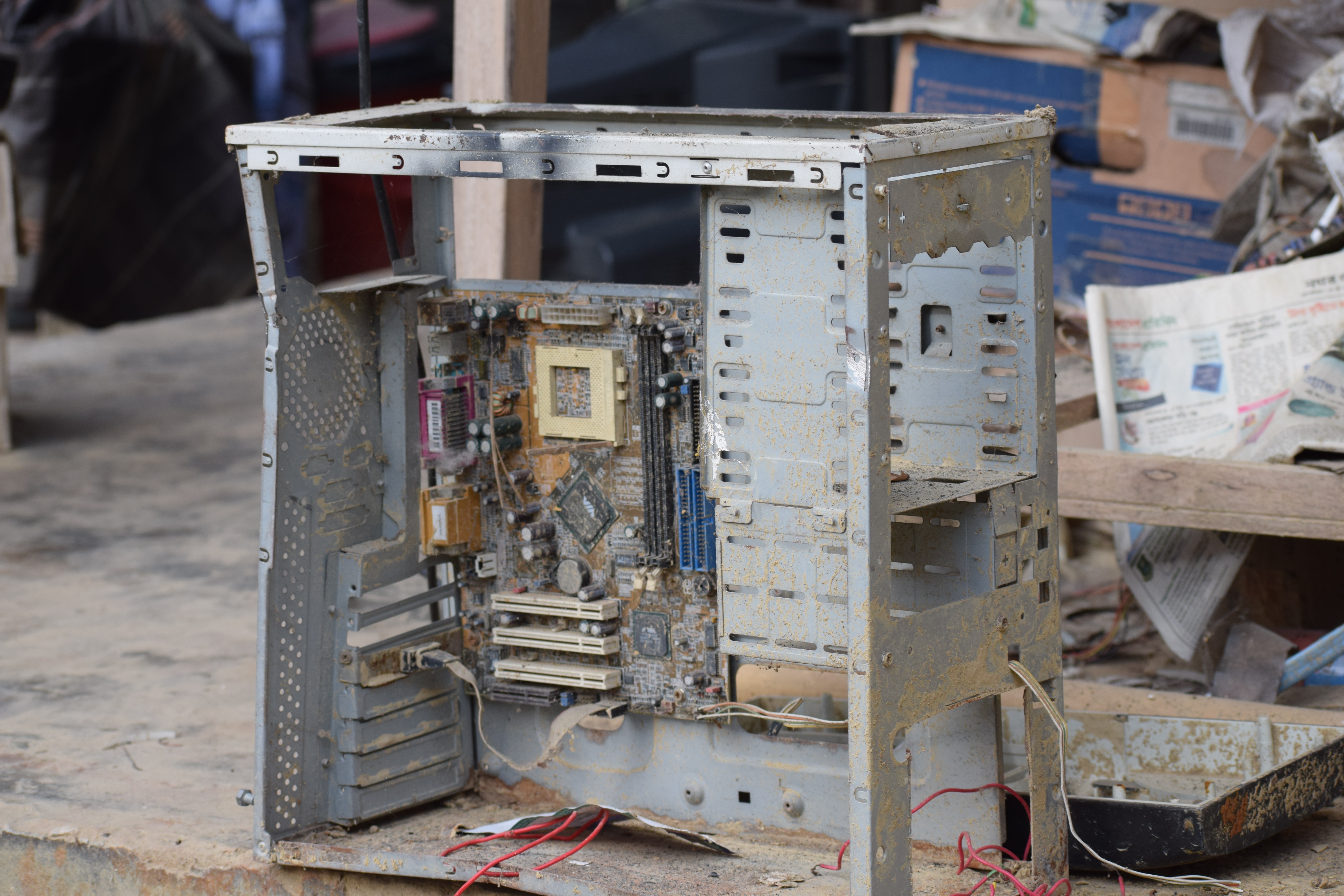
Over the past few years, recycling and e-waste management have become part of the corporate asset management strategy of businesses in the UK and beyond. This is due both to new regulations and recycling targets and to a greater understanding of how different types of waste affect the environment.
What Raw Materials Are Used to Manufacture IT Assets, And Which Can Be Recycled?
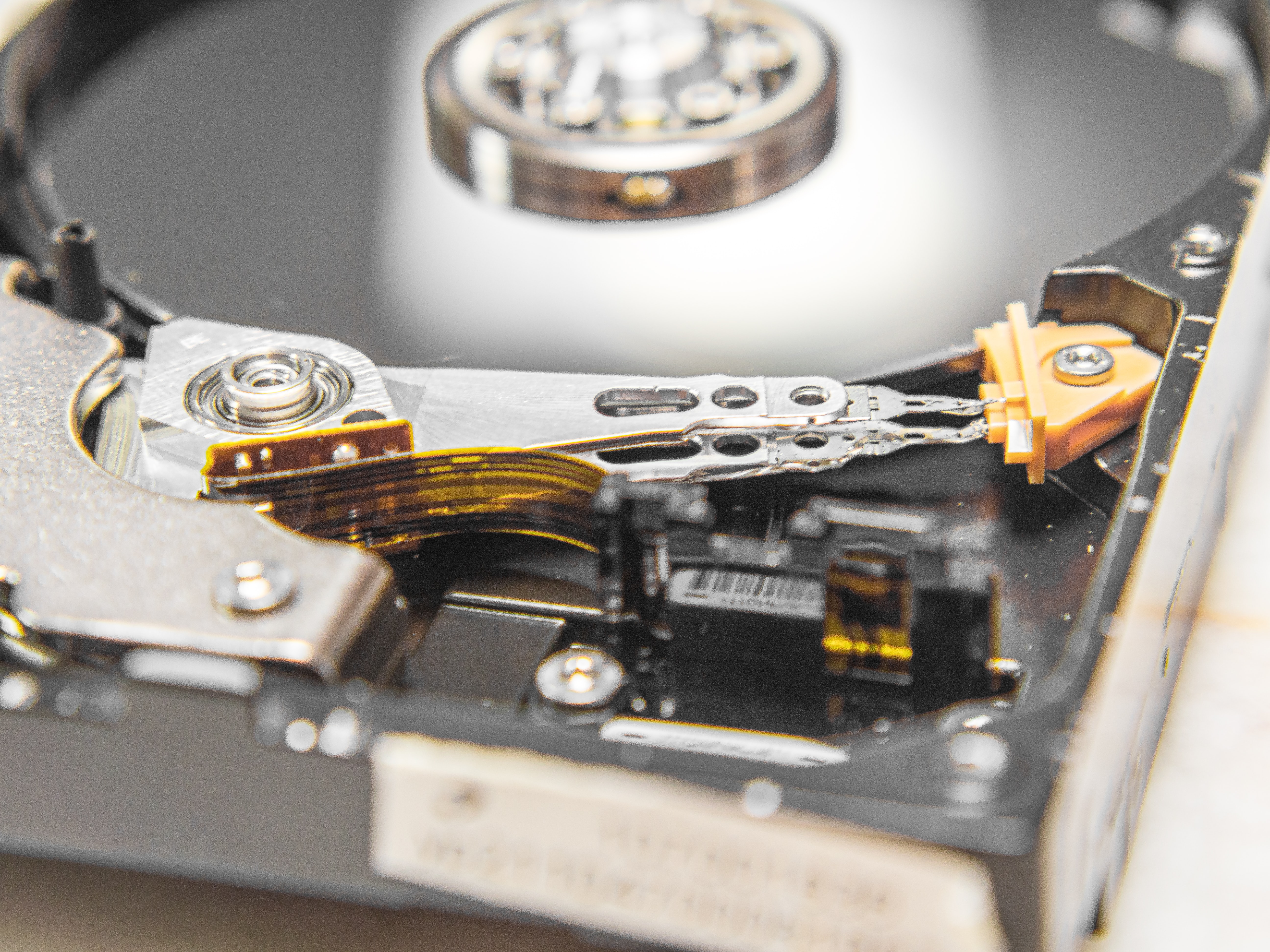
Although the casing of a typical PC, laptop, networking switch or router might be made from plastic, there are many metallic elements below the surface, most of which can be recycled and reclaimed. Some of these materials are environmentally toxic if they end up in landfill so, just like consumer electronic devices, there are strict guidelines and best practices in place for disposing of IT...
What Is Causing The Global Microchip Shortage In 2022?
Global microchip shortages began making headlines in 2020 and are still a growing cause for concern. If you’ve attempted to purchase a new or second-hand car this year, you will no doubt already be aware of the impact the microchip shortage is now having on car supplies and on the price of vehicles. The effect is also being seen on the availability and price of some IT and communication equipment.
3 IT Asset Management Risks Every Business Should Be Aware Of
Keeping IT assets up to date and in good condition is an essential part of ensuring that they remain competitive, function effectively, and are prepared to take full advantage of any emerging software or other technology which has the potential to enhance the way in which they operate.
ITAD Myth Busting – Important Questions To Ask Your IT Asset Disposal Company
If you’re looking for a safe and secure way of disposing of used IT assets, you probably have a shortlist of companies that offer similar services. On the surface, the only difference between many ITAD (Information Technology Asset Disposal) companies is their price point. But there are other important criteria you must consider when choosing an asset disposal company. Below you’ll find 5...
Season Of Goodwill? 5 Crucial Data Sanitisation Questions To Answer Before You Donate Old IT Assets This New Year
The months after Christmas are often a time to have a good clear out. For organisations, upgrading to new IT systems is an excellent opportunity to donate old computers, tablets, and associated hardware to schools or charities, or to sell them on. However, there are a few important considerations to make before pressing go on eBay.
How To Make Your IT Asset Disposal Strategy More Sustainable in 2022
Everybody knows that old technology can damage the environment through its inefficient energy use, but could throwing out your old hardware prematurely in favour of greener tech lead to even more environmental problems? Here are the answers to the top 5 sustainability questions of 2022, and how they could affect your IT asset disposal strategy.
The Importance Of Free Computer Data Destruction In The Protection Of Your Business
Whether you are upgrading your company computers as part of a scheduled refresh or relocating to new commercial premises, you will probably be left with unwanted or non-functional IT hardware.
How Does Your Company Dispose Of Its Computers?
Like many other pre-built tools, old or unwanted computers can be broken down, recycled and given a new lease of life with different owners, or their raw materials repurposed for other consumer items.