When your IT equipment reaches its end of life, your business must decide how to dispose of it ethically and safely. With cybercrime surging, unwanted IT assets can be rich pickings for criminals who are intent on manipulating sensitive data stored on laptops, desktops, mobile phones, or servers. Customers’ personal information, such as bank details, addresses, and purchase history, can provide...
Where to Turn For Safe & Reliable IT Equipment Recycling In Derbyshire
Everything You Need To Know About IT Asset Disposal
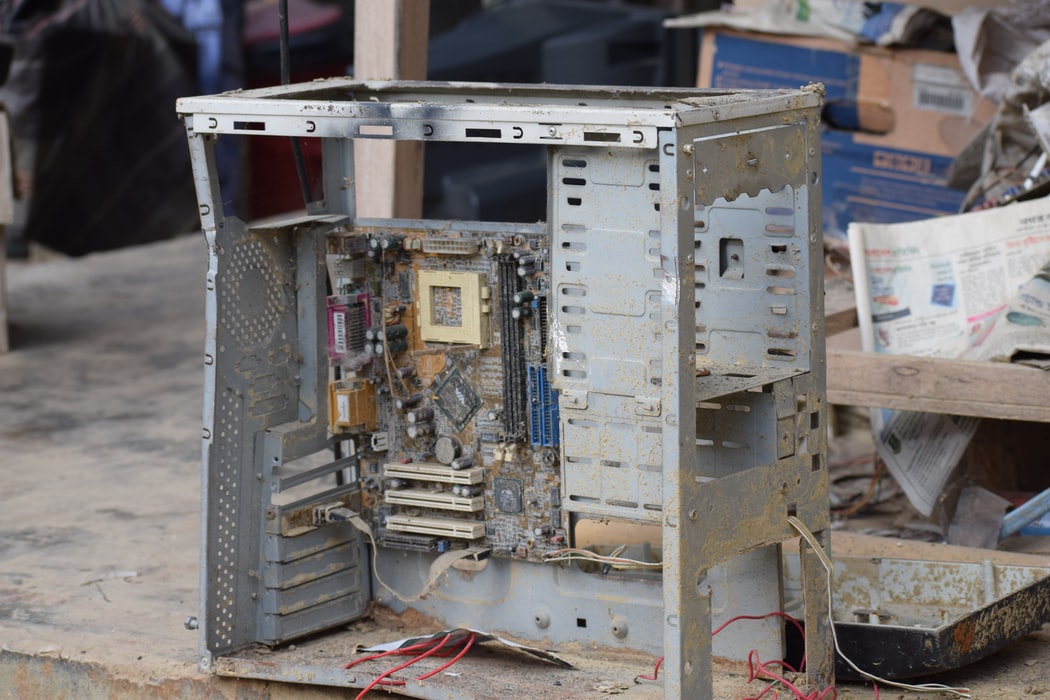
The IT asset disposal process must be handled responsibly to prevent data security breaches and to remain compliant with environmental regulations – and there is no shortage of ‘free IT recycling’ companies willing to help take your disused computer hardware off your hands. However, 'free recycling' is frequently synonymous with refurbishing old equipment for sale in developing world countries...
Free IT Disposals: What Should You Do With Your Old IT Equipment?
Safe and effective IT equipment disposal is as important now as it's ever been. Prevalent environmental concerns mean responsible disposal of all types of electronic waste, IT equipment included, is being placed under the microscope like never before. However, equally near the top of everyone's priority list is the question of data security.
How To Choose The Right IT Asset Disposal Company
IT asset disposal is a crucial element of organisational cybersecurity, and when it comes to data protection, it pays to get it right.
Did You Upgrade Your Hardware In Response To Microsoft Stopping Support For Older Versions Of Office?
Office 365 support and integration for several of its flagship software packages finished from the end of October 2020. Exchange Online, OneDrive and OneDrive Business, and SharePoint Online no longer receive any compatibility updates for old Office software suites.
The Benefits Of Electronic Waste Recycling
Electronic waste is a serious problem in the UK and worldwide. According to the Global E-Waste Monitor report (2019), the UK produces more waste electrical and electronic equipment (WEEE) than any other country except Norway. And, while the volume has fallen in the UK since 2016, WEEE – from computers and lighting to printers and mobile phones – continues to present a real challenge to businesses...
How To Securely Destroy Data
A vital part of data lifecycle management is the destruction of data when it is no longer required, or when the storage device has come to the end of its life.
The Importance Of Recycling Old Computers, And Where You Can Recycle Them!
From desktops and mobile phones, to servers and USB flash drives, IT hardware is a core part of modern business. However, the industry is rapidly advancing, so most organisations must frequently dispose of unwanted IT assets. Knowing where to recycle old computers safely can be a challenge.
A Brief Guide to ‘Zero Waste’ IT: The Advantages and Dangers
Zero Waste is a new and innovative approach to managing the disposal and reuse of outdated, broken, and faulty IT assets. The movement aims to drastically cut down the masses of plastics, rare earth metals, and valuable, still-working components that end up thrown away, burned, or landfilled each year by British businesses each year.
How Can I Dispose of My Old IT Equipment?
Everything made has a 'best before' date, and computers, monitors, and IT assets are no exception. If your company IT equipment is becoming outdated and slow, or is damaged or broken, you're going to want a safe and clean way to dispose of your old equipment to make way for the new.



.jpg)















